Installation guide
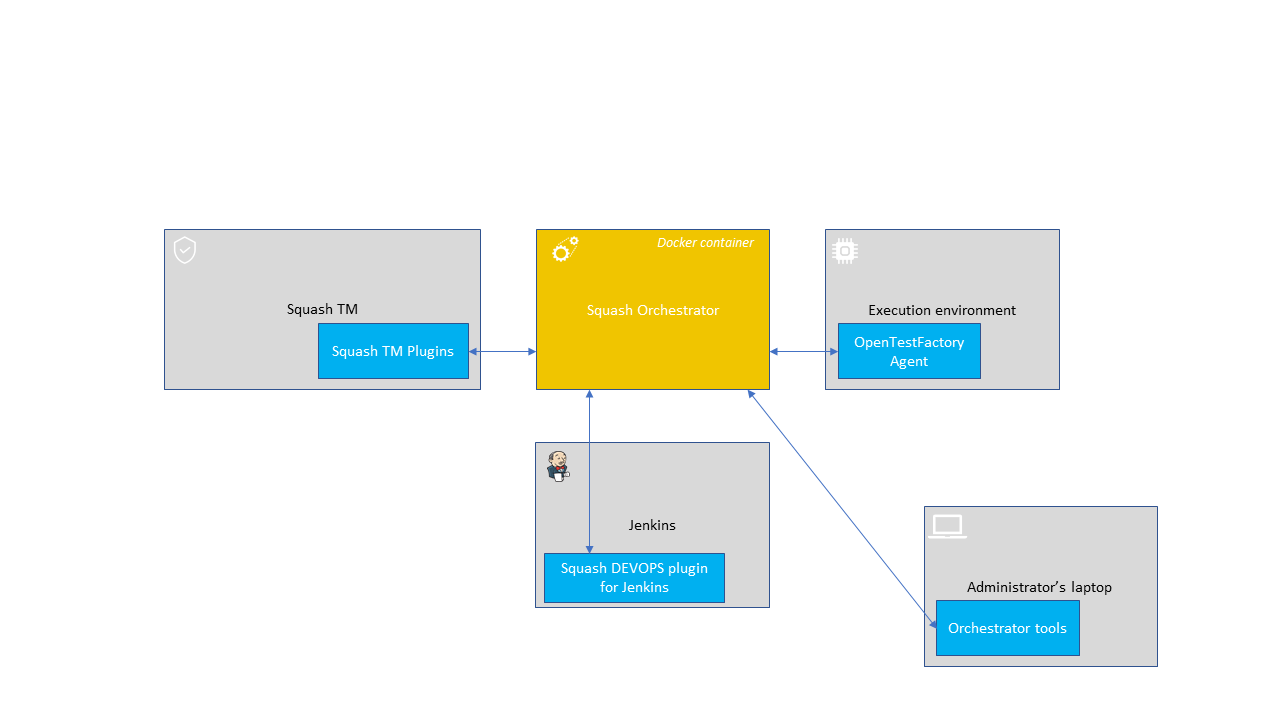
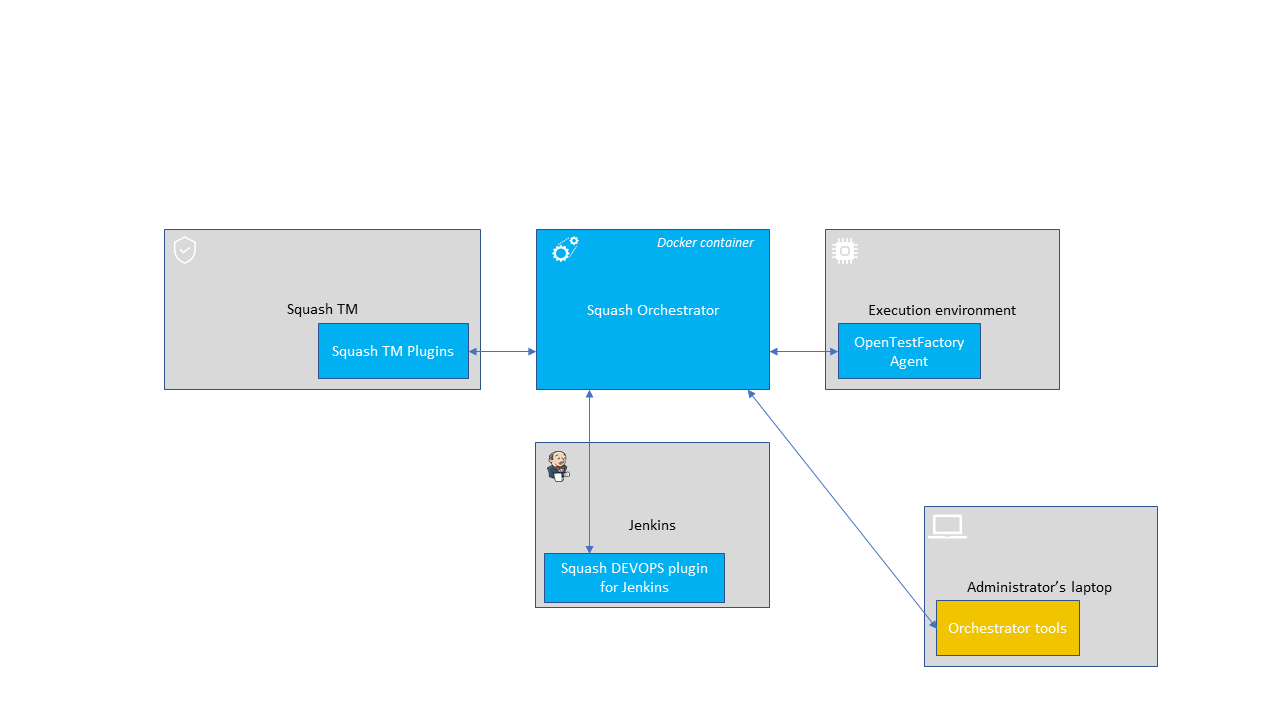
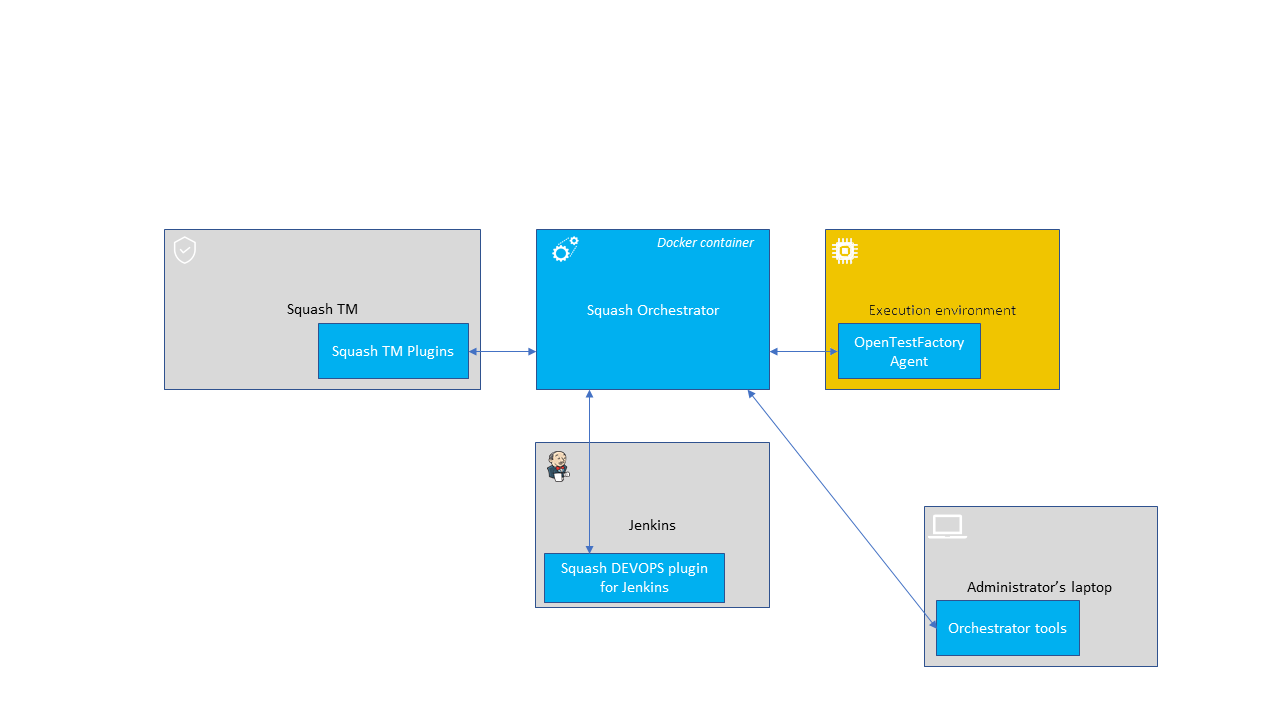
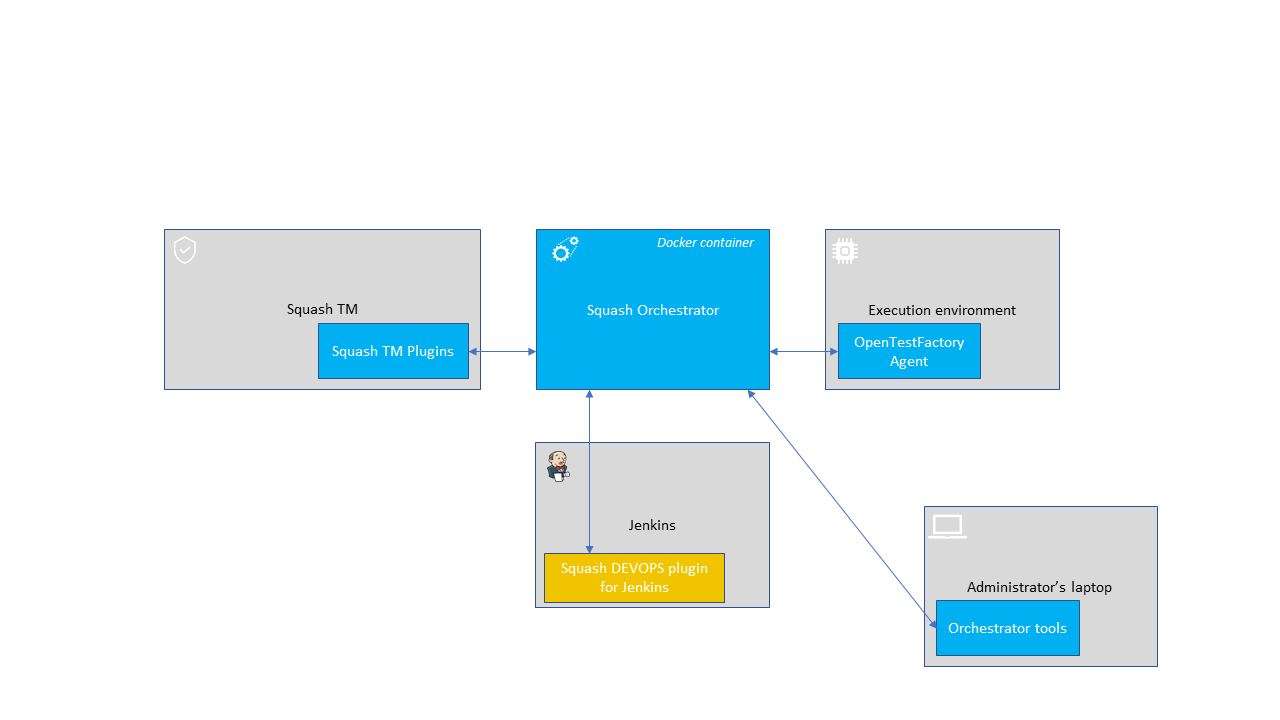
This page describes how to install one by one all the SquashTM components for the support of the automated tests.
Legend
️💎 indicates an Ultimate component or feature. An overview of the Premium and Ultimate features is available here. To benefit from these or to ask for more information, check our website or contact us.
SquashTM Orchestrator
Installation
The installation of SquashTM Orchestrator consists in deploying a Docker image. It contains all core services (part of the OpenTestFactory Orchestrator) and some SquashTM specific services.
To get the latest image of SquashTM Orchestrator, use the following command:
docker pull squashtest/squash-orchestrator:6.2.0
Recommendations for sizing the Docker container are:
- CPU: 1.5
- RAM: at least 1.5 GB
- disk: provide the capacity for storing the execution reports and their attachments for one hour of usage
Trouble shooting - Accessibility of the SquashTM instance
Check that the SquashTM instance is accessible from SquashTM Orchestrator. To do this, go onto the Docker host and run the command (replacing https://squashtm.example.com/squash with the URL of your instance):
curl https://squashtm.example.com/squash/isSquashAlive
SquashTM is Alive!
Usage
Ultimate💎 license setup
The services reserved for SquashTM Ultimate are accessible if you provide the SquashTM Ultimate license squash-tm.lic (the same file as the one used for SquashTM) in the SquashTM Orchestrator container.
This license must be mounted, in the container, in a license subdirectory of the directory defined by the LICENSE_PATH environment variable (i.e. {LICENSE_PATH}/license/squash-tm.lic). If this environment variable is not defined, the license subdirectory of the /app directory (i.e. /app/license/squash-tm.lic) will be used.
Community or Premium👑 license
If you are using SquashTM Community or SquashTM Premium👑, do not declare a license file (you have to ignore the highlighted lines in the command samples below).
Using Docker
The execution of the following command will start the SquashTM Orchestrator using an existing execution environment, with self-generated trusted keys (which is not recommended in a production setup):
docker run -d \
--name orchestrator \
-p 7774:7774 \
-p 7775:7775 \
-p 7776:7776 \
-p 7796:7796 \
-p 38368:38368 \
-p 34537:34537 \
-p 24368:24368 \
-p 12312:12312 \
-e SSH_CHANNEL_HOST=the_environment_ip_or_hostname \
-e SSH_CHANNEL_USER=user \
-e SSH_CHANNEL_PASSWORD=secret \
-e SSH_CHANNEL_TAGS=ssh,linux,robotframework \
-v ./path/to/my/squash-tm.lic:/app/license/squash-tm.lic \
squashtest/squash-orchestrator:6.2.0
docker run -d ^
--name orchestrator ^
-p 7774:7774 ^
-p 7775:7775 ^
-p 7776:7776 ^
-p 7796:7796 ^
-p 38368:38368 ^
-p 34537:34537 ^
-p 24368:24368 ^
-p 12312:12312 ^
-e SSH_CHANNEL_HOST=the_environment_ip_or_hostname ^
-e SSH_CHANNEL_USER=user ^
-e SSH_CHANNEL_PASSWORD=secret ^
-e SSH_CHANNEL_TAGS=ssh,linux,robotframework ^
-v ./path/to/my/squash-tm.lic:/app/license/squash-tm.lic ^
squashtest/squash-orchestrator:6.2.0
docker run -d `
--name orchestrator `
-p 7774:7774 `
-p 7775:7775 `
-p 7776:7776 `
-p 7796:7796 `
-p 38368:38368 `
-p 34537:34537 `
-p 24368:24368 `
-p 12312:12312 `
-e SSH_CHANNEL_HOST=the_environment_ip_or_hostname `
-e SSH_CHANNEL_USER=user `
-e SSH_CHANNEL_PASSWORD=secret `
-e SSH_CHANNEL_TAGS=ssh,linux,robotframework `
-v ./path/to/my/squash-tm.lic:/app/license/squash-tm.lic `
squashtest/squash-orchestrator:6.2.0
It exposes the following services on the corresponding ports:
- receptionist (port 7774)
- observer (port 7775)
- killswitch (port 7776)
- insightcollector (port 7796)
- eventbus (port 38368)
- localstore (port 34537)
- agentchannel (port 24368)
- quality gate (port 12312)
If you do not plan to declare agents, port 24368 may not be exposed. Similarly, if you do not plan to use the quality gate, port 12312 may not be exposed.
Reminder
You can replace /app with your own path and declare this one in the LICENSE_PATH environment variable:
-e LICENSE_PATH=/path/to/my/directory \
-v ./path/to/my/squash-tm.lic:/path/to/my/directory/license/squash-tm.lic \
You can view the logs of the container:
docker logs orchestrator
To delete the container, use the following commands:
docker kill orchestrator
docker rm orchestrator
Using docker-compose
In a new folder, create a data directory in which you will place your public key and the licensesubdirectory with the squash-tm.lic file inside.
+-- dossier
+-- .env
+-- data
| +-- trusted_key.pub
| +-- license
| +-- squash-tm.lic
+-- docker-compose.yml
Also, create an .env file centralizing the versions of the components you will use:
ORCHESTRATOR_VERSION=6.2.0
TOKEN=ey...
Finally, create the following docker-compose.yml file:
# docker-compose up -d
version: "3.4"
services:
# SquashTM Orchestrator
orchestrator:
container_name: orchestrator
image: squashtest/squash-orchestrator:$ORCHESTRATOR_VERSION
restart: always
volumes:
- type: bind
source: ./data/trusted_key.pub
target: /etc/squashtf/squash.pub
- type: bind
source: ./data/license/squash-tm.lic
target: /app/license/squash-tm.lic
ports:
- "7774:7774"
- "7775:7775"
- "7776:7776"
- "7796:7796"
- "38368:38368"
- "34537:34537"
- "24368:24368"
- "12312:12312"
# docker-compose up -d
version: "3.4"
services:
# SquashTM Orchestrator
orchestrator:
container_name: orchestrator
image: squashtest/squash-orchestrator:$ORCHESTRATOR_VERSION
restart: always
volumes:
- type: bind
source: ./data/trusted_key.pub
target: /etc/squashtf/squash.pub
- type: bind
source: ./data/license/squash-tm.lic
target: path/to/my/directory/license/squash-tm.lic
environment:
- LICENSE_PATH=path/to/my/directory
ports:
- "7774:7774"
- "7775:7775"
- "7776:7776"
- "7796:7796"
- "38368:38368"
- "34537:34537"
- "24368:24368"
- "12312:12312"
To launch SquashTM Orchestrator, go to this folder and use the following command:
docker compose up -d
You can view the logs of this deployment using the following command:
docker compose logs
To stop SquashTM Orchestrator, go in the folder and use the following command:
docker compose down
Using Kubernetes
The following example deploys a pod containing SquashTM Orchestrator.
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: squash-autom
name: squash-autom
spec:
replicas: 1
selector:
matchLabels:
app: squash-autom
template:
metadata:
labels:
app: squash-autom
spec:
containers:
- name: orchestrator
image: squashtest/squash-orchestrator:6.2.0
imagePullPolicy: Always
ports:
- containerPort: 7774
protocol: TCP
- containerPort: 7775
protocol: TCP
- containerPort: 7776
protocol: TCP
- containerPort: 7796
protocol: TCP
- containerPort: 38368
protocol: TCP
- containerPort: 34537
protocol: TCP
- containerPort: 24368
protocol: TCP
- containerPort: 12312
protocol: TCP
resources:
limits:
memory: 1.5G
requests:
cpu: "1.5"
memory: 1.5G
volumeMounts:
- mountPath: /etc/squashtf
name: squash-orchestrator-trusted-key
- mountPath: /app/license
name: squash-license
volumes:
- name: squash-orchestrator-trusted-key
secret:
defaultMode: 420
secretName: trusted-keys
- name: squash-license
secret:
secretName: squash-license
---
apiVersion: v1
kind: Service
metadata:
name: squash-autom
spec:
selector:
app: squash-autom
ports:
- name: receptionist
port: 7774
protocol: TCP
targetPort: 7774
- name: eventbus
port: 38368
protocol: TCP
targetPort: 38368
- name: localstore
port: 34537
protocol: TCP
targetPort: 34537
- name: observer
port: 7775
protocol: TCP
targetPort: 7775
- name: killswitch
port: 7776
protocol: TCP
targetPort: 7776
- name: insightcollector
port: 7796
protocol: TCP
targetPort: 7796
- name: agentchannel
port: 24368
protocol: TCP
targetPort: 24368
- name: qualitygate
port: 12312
protocol: TCP
targetPort: 12312
To deploy this pod and service on your Kubernetes cluster, create a namespace (or use an existing namespace):
kubectl create namespace my-namespace
Then, create secrets containing your public key and the license, deploy this secrets in the namespace you just created:
kubectl create secret generic trusted-keys --from-file=trusted_key.pub=trusted_key.pub --namespace my-namespace
kubectl create secret generic squash-license --from-file=squash-tm.lic=squash-tm.lic --namespace my-namespace
Finally, deploy the pod and the service:
kubectl apply -f squash-autom.yaml --namespace my-namespace
To delete the pod, use the following command:
kubectl delete -f squash-autom.yaml --namespace my-namespace
Configuration with pre-generated keys
Outside of experimentation, it is recommended to start SquashTM Orchestrator by specifying one or more public keys that will be used to validate tokens authenticating incoming requests.
The following commands generate a pair of trusted_key.pem / trusted_key.pub keys (you can generate several if you wish):
openssl genrsa -out trusted_key.pem 4096
openssl rsa -pubout -in trusted_key.pem -out trusted_key.pub
If your public keys (*.pub) are in a public_keys directory, here is an example making them accessible to the orchestrator (all files in this directory will be accessible to the orchestrator, do not put your private keys there):
docker run ... \
-v /path/to/public_keys:/etc/squashtf \
...
docker run ... ^
-v d:\path\to\public_keys:/etc/squashtf ^
...
docker run ... `
-v d:\path\to\public_keys:/etc/squashtf `
...
If you plan to use only one public key, you can make it accessible directly:
docker run ... \
-v /path/to/public_keys/trusted_key.pub:/etc/squashtf/trusted_key.pub \
...
docker run ... ^
-v d:\path\to\public_keys/trusted_key.pub:/etc/squashtf/trusted_key.pub ^
...
docker run ... `
-v d:\path\to\public_keys/trusted_key.pub:/etc/squashtf/trusted_key.pub `
...
Tokens verified by these keys will have full access to the default namespace. This behavior can be changed by modifying the image configuration.
For more details about SquashTM Orchestrator configuration, please check the OpenTestFactory Orchestrator documentation on which SquashTM Orchestrator is based (the deployment of the two orchestrators is similar). That documentation also details the specific cases of deploying with docker-compose or with Kubernetes.
Using self-signed certificates
A FAQ details how to use SquashTM Orchestrator with self-signed certificates.
Orchestrator tools
Installation
The orchestrator tools aim at simplifying the use of that one. They can be installed on any machine from where we want to administrate the orchestrator.
They require Python 3.8 or later. They are usable on Linux, maxOS, or Windows.
These tools can be installed from PyPI by using the following command:
pip install --upgrade opentf-tools
Overview of the tool capabilities
opentf-readywaits until the orchestrator is ready to accept workflows.opentf-donewaits until the orchestrator can be safely stopped (i.e. it has no more pending tasks).opentf-ctlcan be used to- start / track / stop a workflow
- generate a signed token
- list the agents
- generate / modify a configuration file
- …
Generating a signed token
Requests to SquashTM Orchestrator must be associated with signed tokens.
Given a trusted_key.pem private key in the current directory, the following command generates a signed token that will be recognized by the orchestrator if it knows the corresponding public key:
opentf-ctl generate token using trusted_key.pem
Please specify an algorithm (RS512 if unspecified):
The specified algorithm is: RS512
Please enter the issuer (your company or department): acme
Please enter the subject (you or the person you are making this token for): charlie
The signed token is:
ey...
Details
A complete description of the tools is available in the OpenTestFactory documentation.
OpenTestFactory Agent
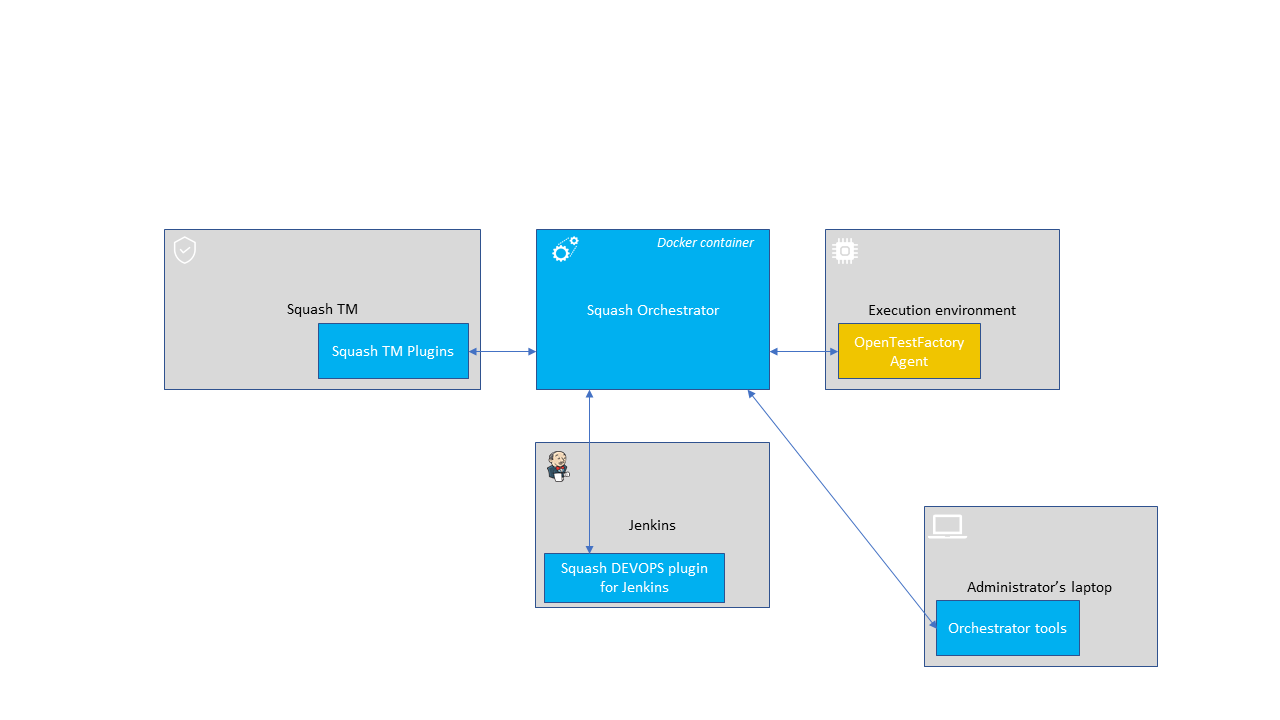
Installation
The OpenTestFactory agent is a Python application that is installed in the execution environment. It requires Python 3.7 or higher. It works on Linux, macOS, and Windows.
The agent is a simple script. It only has one external dependency, the well known requests Python library (it will be installed if not already present on the execution environment).
To install the agent from PyPI, use the following command:
pip install --upgrade opentf-agent
You can test your installation by running the following command:
opentf-agent --help
Usage
Summary
$ opentf-agent --help
usage: opentf-agent [-h] --tags TAGS --host HOST [--port PORT] [--path_prefix PATH_PREFIX] [--token TOKEN] [--encoding ENCODING] [--script_path SCRIPT_PATH] [--workspace_dir WORKSPACE_DIR] [--name NAME] [--polling_delay POLLING_DELAY] [--liveness_probe LIVENESS_PROBE] [--retry RETRY] [--debug]
OpenTestFactory Agent
optional arguments:
-h, --help show this help message and exit
--tags TAGS a comma-separated list of tags (e.g. windows,robotframework)
--host HOST target host with protocol (e.g. https://example.local)
--port PORT target port (default to 24368)
--path_prefix PATH_PREFIX
target context path (default to no context path)
--token TOKEN token
--encoding ENCODING encoding on the console side (defaults to utf-8)
--script_path SCRIPT_PATH
where to put temporary files (defaults to current directory)
--workspace_dir WORKSPACE_DIR
where to put workspaces (defaults to current directory)
--name NAME agent name (defaults to "test agent")
--polling_delay POLLING_DELAY
polling delay in seconds (default to 5)
--liveness_probe LIVENESS_PROBE
liveness probe in seconds (default to 300 seconds)
--retry RETRY how many time to try joining host (default to 5,
0 = try forever)
--debug whether to log debug informations.
Example
Assuming there is a SquashTM Orchestrator running on orchestrator.example.com, with a known token stored in the TOKEN environment variable, the following command will register the Windows-based execution environment and will possibly receive commands from SquashTM Orchestrator targeting windows and/or robotframework tagged environments:
chcp 65001
opentf-agent --tags windows,robotframework --host http://orchestrator.example.com/ --token %TOKEN%
The agent will poll the Orchestrator every 5 seconds, and will execute the received commands.
The chcp command sets the console to Unicode. It is Windows-specific. It is not mandatory but may be needed depending on the test framework available in the execution environment.
Details
A complete description of the agent is available in the OpenTestFactory documentation.
Execution environments
Some test technologies require that some particular components are installed in the execution environment, these ones are indicated in the pages describing the specificities of each technology.
Plugin for Jenkins
Deprecation of the Plugin for Jenkins
The Plugin for Jenkins is deprecated.
Starting with Squash Orchestrator 2024-11, it will not support the latest SquashTM Orchestrator features.
With SquashTM 12.0 / SquashTM Orchestrator 2025-12, it will not be released anymore.
Jenkins will have to use opentf-ctl as described in the OpenTestFactory documentation.
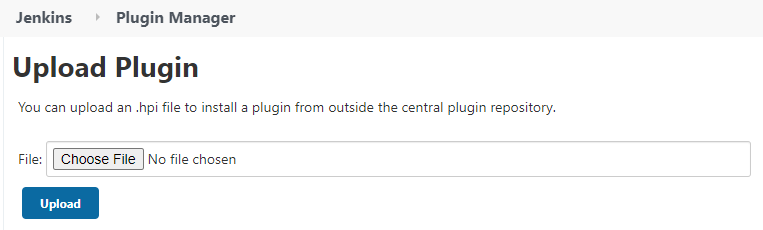
Installation
The plugin is freely downloadable, as a .hpi file (opentestfactory-orchestrator-2.2.0.hpi).
To install it, you have to submit the plugin in the Upload Plugin area accessible by the Advanced tab of the Plugin Manager in Jenkins configuration:
Compatibility of the plugin
This plugin is compatible with version 2.357 or higher of Jenkins.
Java version
Versions 2.0.0 and later of the Plugin for Jenkins requires Java 11 which is also necessary for Jenkins 2.357 or later (see Jenkins announcement). This means that
- if you use Jenkins version 2.357 or later, you must use the Plugin for Jenkins 2.0.0 or later;
- otherwise, you must use a version 1.X.Y of the Plugin for Jenkins (which is compatible with versions 2.164.1 up to 2.356 of Jenkins); the last such version, opentestfactory-orchestrator-1.4.0.hpi, is downloadable here.